Achieve the full benefits of your Okta Cloud investment with our Expert Okta Consultants and comprehensive support packages. Call Today (888) 959-2825
Our Okta Clients


Reasons for considering us.
- Reduce the time needed to ramp up new IT Admin Staff to learn the Okta Identity Engine complexities.
- Always Available Support for Unwavering Success.
- Our team can seamlessly integrate and jump into your Okta instance with your existing IT infrastructure, minimizing disruptions and ensuring a smooth transition.
- Identify opportunities to leverage Okta's advanced features for your business.
- Expertise at Your Fingertips: Our team of Senior Okta consultants possesses in-depth knowledge of the platform and a demonstrated history of successful implementations.
What Makes An Exceptional Okta Consulting Engineer For Your Needs?
Our Engineers
Our Okta Certified Consulting engineers understand our critical role in helping organizations like yours implement and optimize your Identity and Access Management (IAM) strategies using the Okta platform. To ensure a successful engagement, here are some of the key traits we bring to the table:

Beyond Cyber
We go beyond cyber technical expertise. Our communication and interpersonal skills ensure we collaborate effectively with clients across various technical and non-technical backgrounds. We are easy to work with.
Client-Centric
We prioritize your needs and satisfaction. We work collaboratively to understand your specific challenges and goals, delivering solutions that address them effectively.
Deep Okta Expertise
We possess in-depth knowledge of Okta, encompassing its features, functionalities, and underlying architecture. We hold relevant certifications like Okta Certified Professional (OCP) or Okta Certified Architect (OCA) to validate our expertise.
Cloud Savvy
We are familiar with cloud-based infrastructure and APIs, crucial for seamless Okta deployments in today's cloud-centric landscape.
You're Missing Out On Your Okta Cloud Purchase!
Timely Expert Support
When purchasing your Okta licenses directly from Okta, you miss out on something important—timely, expert-quality support and knowledge.
Strong Work Ethic and Independence
We take ownership of projects, managing them with dedication and initiative.
Wider IAM and Cloud App Landscape
Understanding various Cloud and IAM solutions allows us to compare and contrast options, ensuring the best fit for your organization.
Teamwork and Collaboration
We believe in working effectively with other engineers, consultants, and clients to achieve the best possible outcome.
Videos
Why Do Customers Need A Okta Managed Service?
Knowledge
Access expert advice and guidance to optimize resources, streamline processes, and enhance efficiency.
Optimize Costs
Decrease IT expenditures and enhance the cost-efficiency of technical operations.
Address your business requirements faster.
Acquire tailored solutions designed to meet your distinct business needs and objectives.
Implement New Technologies quickly.
Implement and manage new cloud applications and technology with ease.
Our Support!
We're here for you every step of the way - whether it's answering your call, chatting with you on Slack, or meeting you wherever you need us!
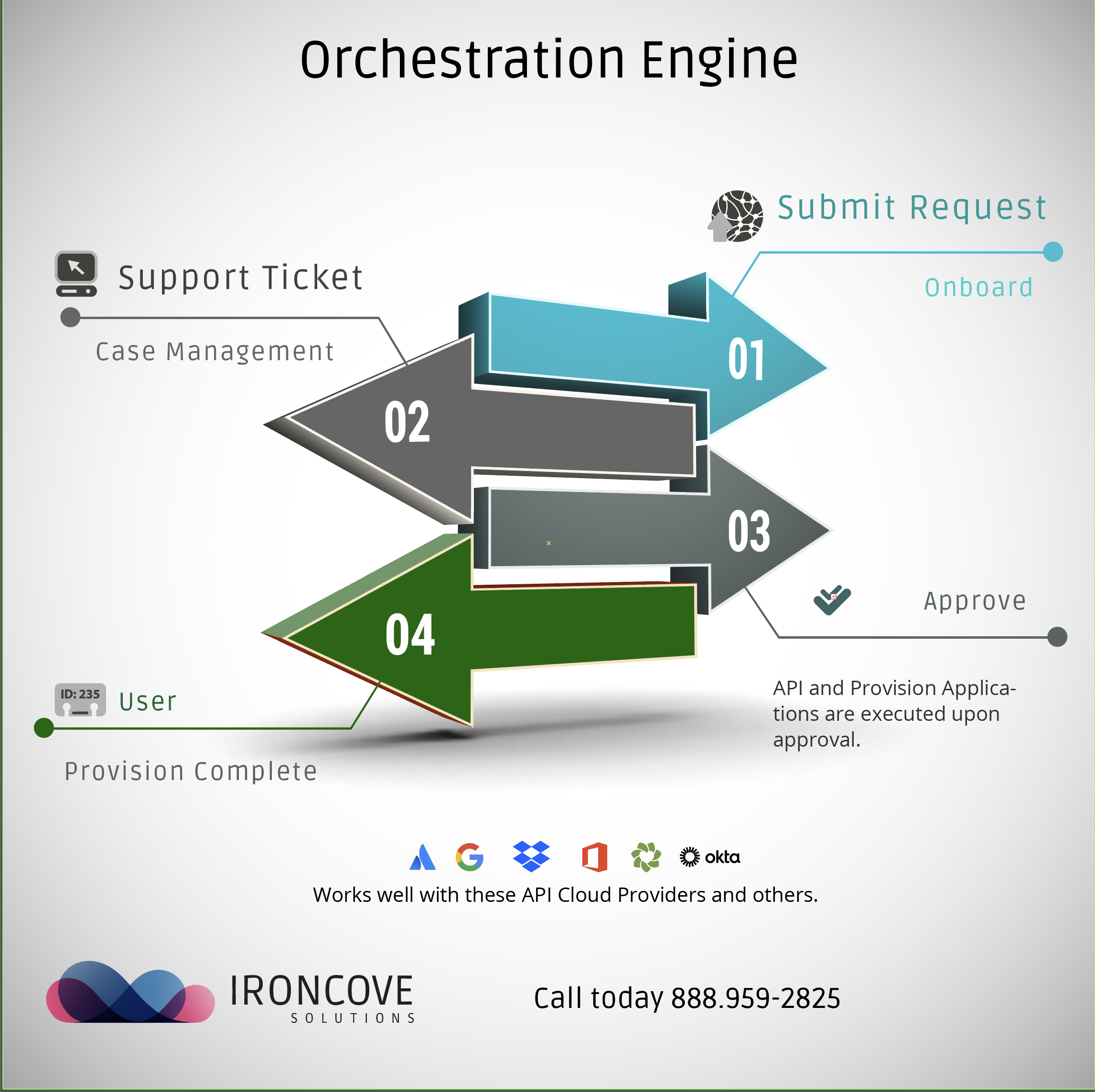
Save Time With Our Orchestration Engine For Okta Workflows
Save 30 Minutes or more for onboarding workers to Cloud Applications.
OE is a customized and convenient application, single web page, and one-stop-place for owners and managers to onboard and offboard users to business cloud applications. No more looking for where to turn workers on or off. A one-stop web page to on and off board workers, partners and users. Save Time